The way people interact with technology is changing—once again. Just as websites gave way to mobile applications, the next major shift is already underway. Users no longer navigate complex interfaces...
Read MoreCyren Threat Intelligence
Cyren stops
How does Cyren Threat Intelligence work
Cyren protects hundreds of millions of users
against emerging threats every minute.






Cyren Website URL Category Checker
As we analyze global threats to data security, each URL is classified into a category based on a variety of information – Use our Website URL Category Checker to view current categories.
Cyren Threat Detection and Intelligence
URL Categorization
Email Security
Inbox Protection
Threat Intelligence
Malware Detection
TacitRed
Cyren Threat Intelligence FAQs
Is Cyren Threat Intelligence fully operational under Data443?
Yes. Cyren Threat Intelligence is fully operational and actively enhanced as part of the Data443 security portfolio, with ongoing investment in platform stability, integrations, and threat coverage.What is Cyren Threat Intelligence?
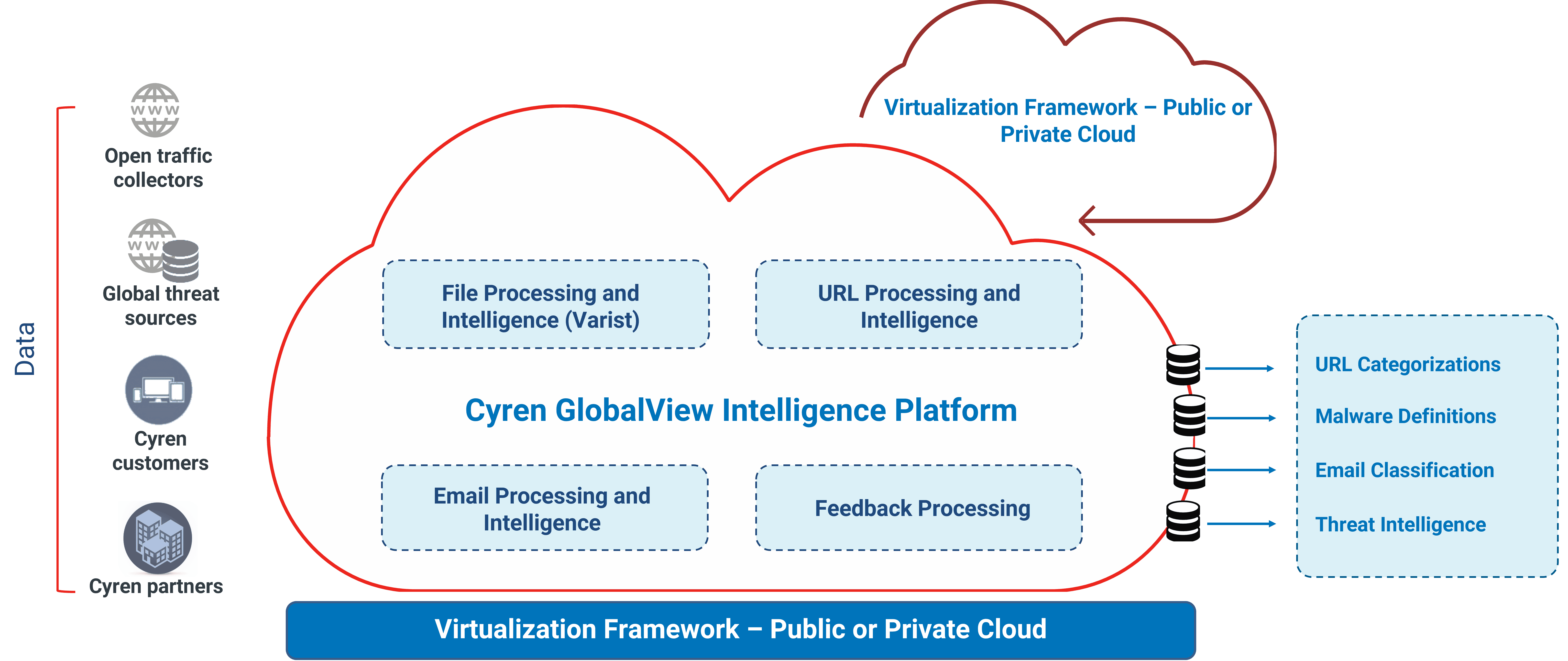
Cyren Threat Intelligence by Data443 delivers real-time threat data on malware, phishing, spam, and malicious IPs or URLs to help organizations detect and block cyber threats faster.How does Cyren Threat Intelligence work?
It processes billions of daily email and web transactions to identify malicious patterns and distributes up-to-date threat feeds through API or FTP in real time.What makes Cyren’s threat detection different?
Cyren’s GlobalView cloud analyzes global traffic at scale, providing contextual, high-fidelity data — including IP reputation, geolocation, and threat relationships — not just static lists.Can I integrate Cyren Threat Intelligence with existing systems?
Yes. It integrates easily via API or JSON feeds with SIEM, SOAR, firewalls, and other cybersecurity tools to enhance your existing defenses.Who uses Cyren Threat Intelligence?
It’s trusted by ISPs, email providers, security vendors, and enterprises that need large-scale, real-time threat visibility across networks.What kinds of threats does Cyren detect?
Cyren identifies phishing sites, malware files, spam campaigns, botnet IPs, and other indicators of compromise across email and web traffic.Is there a trial or evaluation available for Cyren Threat Intelligence?
Yes. Data443 provides a 30-day evaluation of the Threat InDepth feeds so organizations can test coverage and integration before purchasing.How often is the threat intelligence updated?
The feeds update continuously in real time as the global network detects and classifies new threats and malicious hosts.Discover More About Cyren Threat Intelligence
MOVEit Strikes Again: How to Respond to MFT Risk
If it feels like you’ve read this headline before, you probably have. Managed File Transfer (MFT) platforms keep making the news—not just once, but repeatedly. In the last few cycles...
Read MoreSmart Email Archiving, Real Cyber Security with Data443
Threat intelligence combined with mobile application security is the way to go for vulnerable apps. Plus technologies like URL threat lookup and real-time threat detection work together to detect and...
Read MoreYou Might Also Find This Interesting
Data Identification Manager™
Malware, spyware, rootkits, bots, trojans, and any other types of internet security threats
Access Control Manager™
Passwordless Access Control for
the Enterprise
Data Classification
Scan a file for classification of 1300+ global sensitive data policies in 40+ languages within seconds
Data Hound™
Free Live Data Classification for Sample Reporting