TacitRed IOC Automation for CrowdStrike Falcon
Automate IOC distribution from TacitRed to CrowdStrike Falcon, turning threat intelligence into real-time endpoint enforcement.
Designed for enterprise security teams · Built for real-time enforcement


Why Integrating TacitRed IOC Automation
with CrowdStrike Falcon Matters
Threat intelligence doesn’t help if it isn’t enforced.
Many security teams identify high-risk indicators — but still rely on manual IOC uploads, CSV files, or ad-hoc scripts to push those indicators into their EDR.
Integrating TacitRed IOC Automation with CrowdStrike Falcon creates a direct, automated pathway from threat intelligence to endpoint enforcement. Instead of relying on slow, manual IOC uploads that quickly fall behind real-time threats, TacitRed continuously delivers validated, high-confidence indicators directly into Falcon.
This removes the “last-mile” bottleneck and ensures CrowdStrike Falcon applies the latest detections and prevention policies across all endpoints the moment threats are identified.
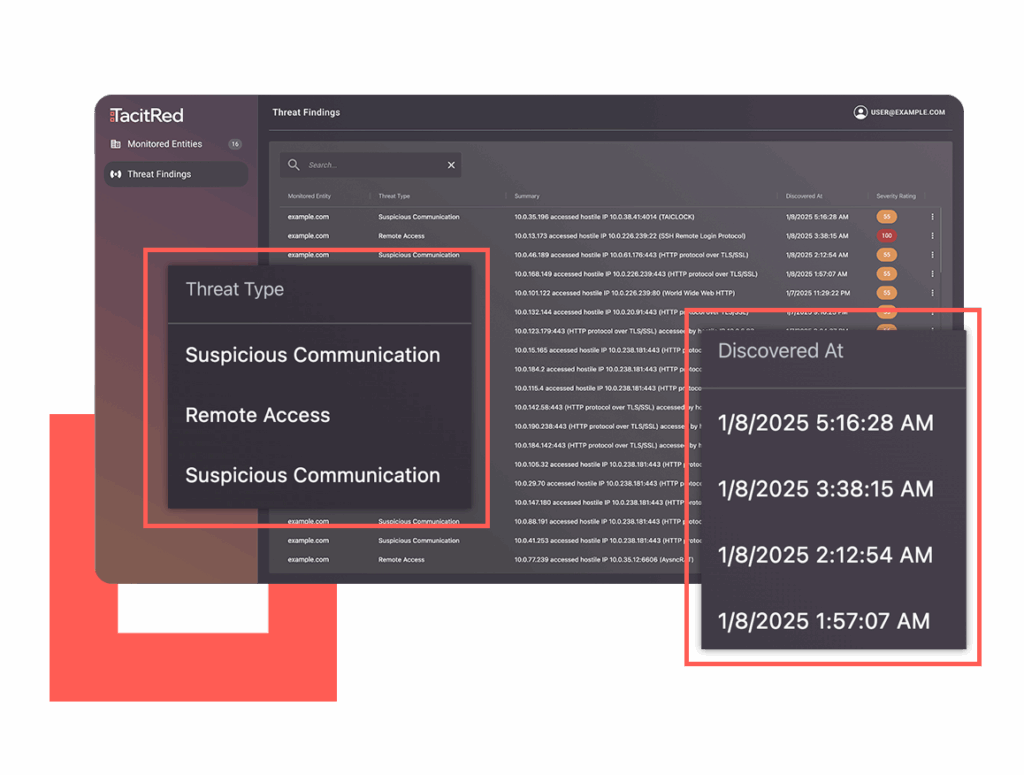
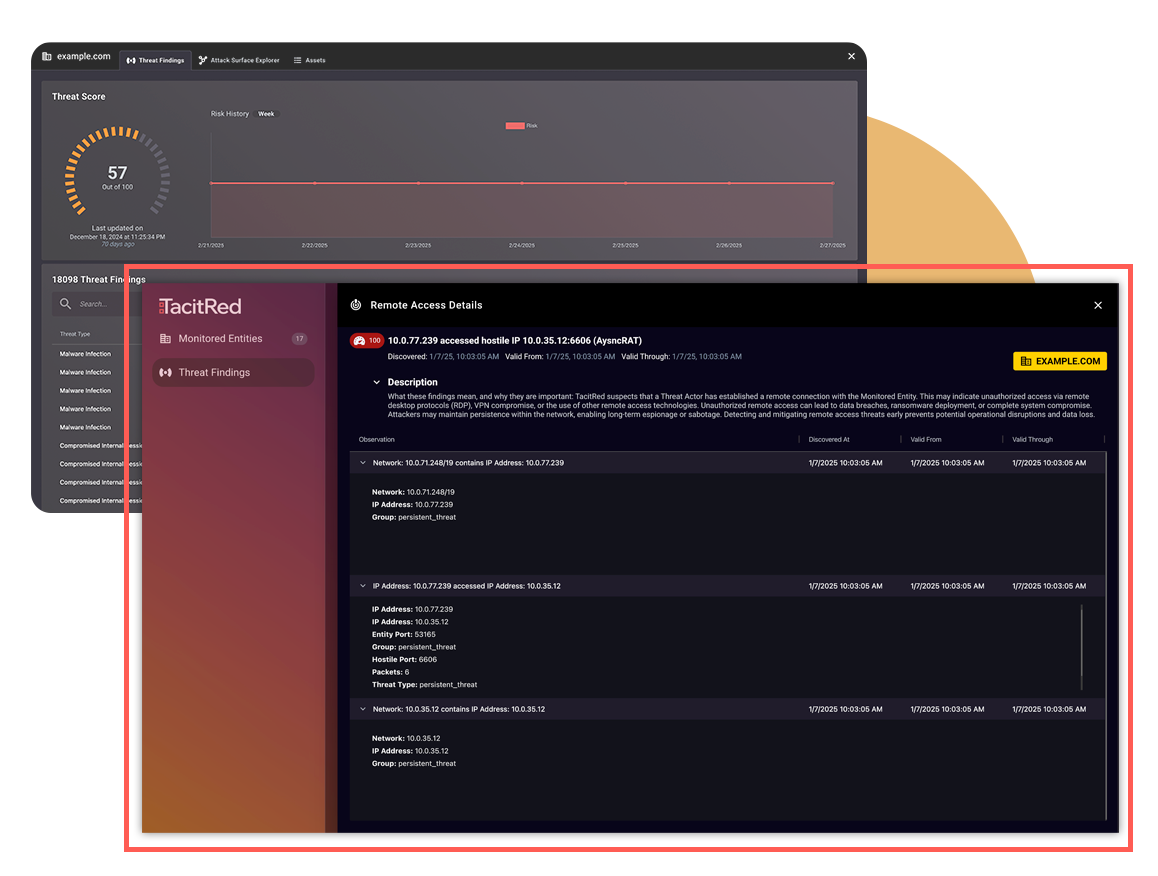
TacitRed Threat Intelligence for CrowdStrike Falcon
Key Capabilities
One-click automation that turns TacitRed findings into live, enforceable IOCs inside CrowdStrike Falcon—ensuring real-time protection without manual effort.
Instant Protection
High-confidence TacitRed indicators are published to Falcon within minutes.Zero Manual Uploads
Stop using CSVs, scripts, or manual workflows.Consistent Enterprise Enforcement
All endpoints receive the same threat intelligence simultaneously.- Design-Partner Friendly
Perfect for early adopters wanting accelerated evaluations.
How It Works
Key Features

Automated IOC Lifecycle
TacitRed indicators are automatically created or updated inside CrowdStrike Falcon, ensuring Falcon always enforces the latest threat intelligence.
Precision Filtering
Send only the indicators that matter—filter by severity, confidence level, indicator type, or activity state to avoid noise in Falcon.

Accurate Field Mapping
TacitRed metadata (type, value, description, severity, timestamps) is cleanly mapped to the CrowdStrike IOC schema for complete context and consistent enforcement.

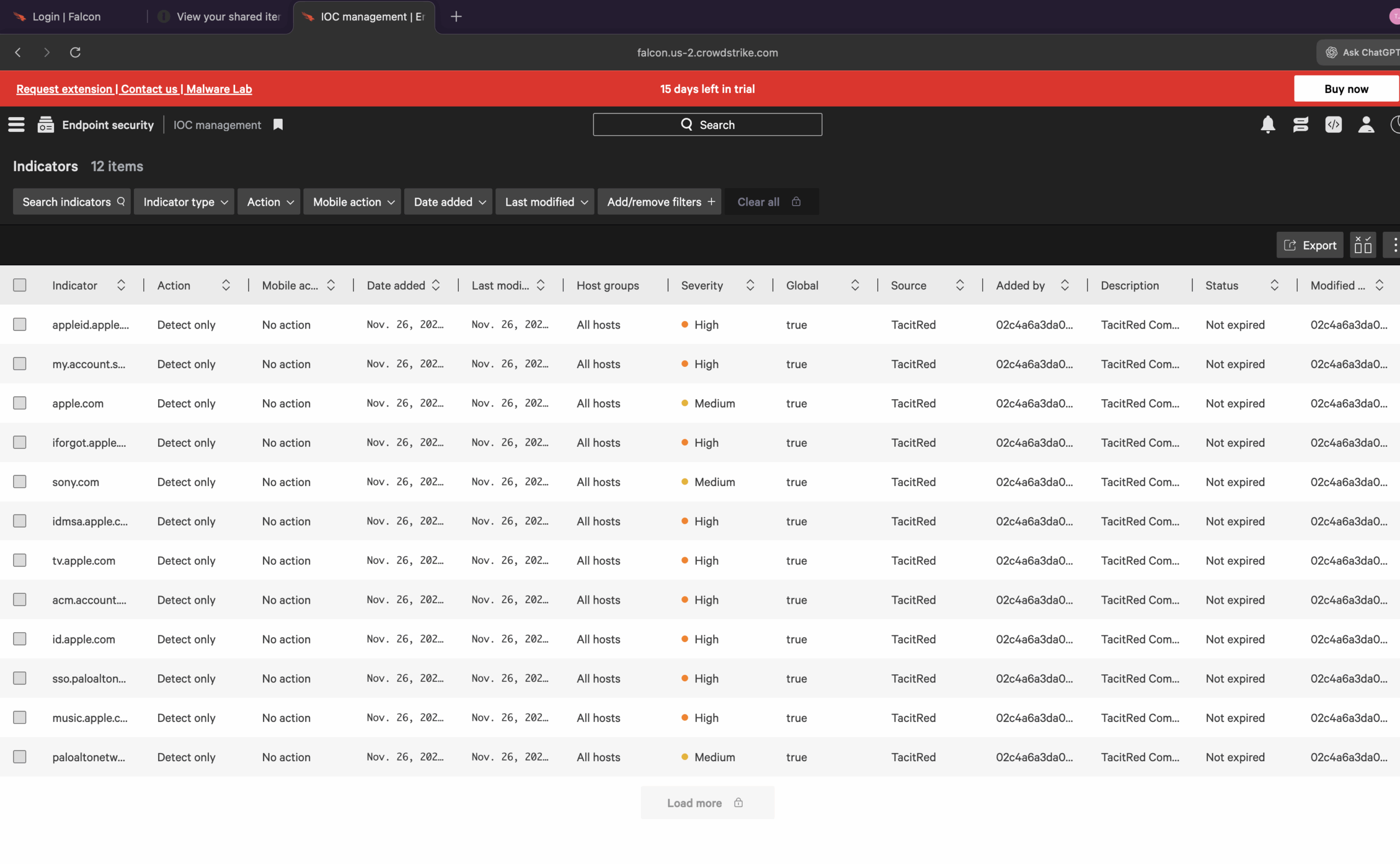
Operational Visibility
All activity remains auditable—IOC creation and updates are visible both in TacitRed and the Falcon IOC management view, supporting compliance and investigation workflows.

Extend
Broaden your visibility into the risk posture of third-party relationships. Enter domains of vendors, suppliers, and partners to uncover their threat landscape, share threat scores, and enable targeted remediation.
Automate your threat enforcement pipeline with
TacitRed Threat Intelligence + CrowdStrike Falcon.
Built for Enterprise SOC Workflows
Why Security Teams Choose TacitRed IOC Automation
TacitRed IOC Automation removes the operational gap between threat detection and endpoint enforcement by automatically delivering high-confidence indicators from TacitRed into CrowdStrike Falcon without manual workflows or delays.

Automatic Intelligence-to-Enforcement Flow
TacitRed identifies high-confidence indicators and automatically creates or updates IOCs in CrowdStrike Falcon, ensuring protections are enforced the moment threats are identified.

End-to-End IOC Lifecycle Automation
From indicator creation to updates, the entire IOC lifecycle is automated, eliminating CSV uploads, scripts, and manual maintenance.
Precision Filtering for High-Confidence Enforcement
Control exactly which indicators are sent to Falcon by filtering on severity, confidence level, indicator type, or activity state — reducing noise and false positives.

Accurate Field Mapping and Context
TacitRed metadata (type, value, description, severity, timestamps) maps cleanly to the CrowdStrike IOC schema, ensuring consistent, context-rich enforcement.
Seamless Installation, Onboarding & Trial Experience
Prerequisites:
A TacitRed account with access to findings and indicators
A CrowdStrike Falcon tenant with API client/secret and IOC write permissions
Quick Installation Steps:
- Deploy the TacitRed → CrowdStrike automation workflow (Logic App, function, or playbook) into your integration environment.
Configure TacitRed API credentials and CrowdStrike API credentials within the workflow.
Set your preferred indicator types, severity thresholds, and any advanced filters (e.g., only active, high-confidence, or specific IOC categories).
Trial Approach:
Start with a limited subset of IOCs (certain categories or severities).
Monitor impact in Falcon and adjust filters before scaling to full coverage.