Protecting your brand is key to success and trust. With more online platforms and digital threats emerging every day, companies are more vulnerable to fraud, brand misuse and other cybercrime....
Read MoreCyren Threat InDepth Feeds
Stop cyber attacks before they hit with real-time feeds on malware, phishing URLs, and malicious IPs


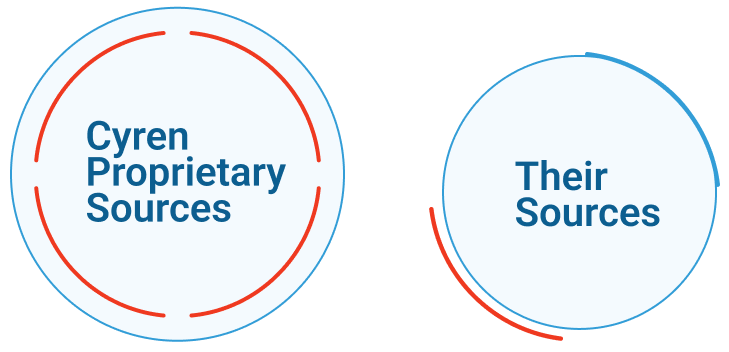
Cyren Threat InDepth is a real-time threat intelligence feed service that gives security teams fresh, high-fidelity data on malware files, phishing URLs, and malicious IP addresses — sourced exclusively from Cyren’s own detection infrastructure, not recycled from shared vendor pools. While most threat intelligence vendors purchase data from the same sources and repackage it, Cyren gathers intelligence directly by analyzing billions of daily transactions across email content, web traffic, and file activity — so your team gets actionable signals before threats become widespread.
Available as API-integrated data feeds, Threat InDepth plugs into your existing security stack to continuously surface emerging threats across three key areas: malware file and URL detection, phishing and fraud URL analysis, and IP reputation intelligence.
DRPS stretch detection and monitoring activities outside of the enterprise perimeter by searching for threats to enterprise digital resources, such as IP addresses, domains and brand-related assets. DRPS solutions provide visibility into the open (surface) web, dark web and deep web environments by providing contextual information on threat actors and the tactics and processes that they exploit to conduct malicious activities.
Why Threat InDepth
Most threat intelligence vendors purchase data from similar sources before repackaging and selling it. Valuable information gets buried within mountains of old information and false positives.
Malware File and URL Intelligence
Phishing and Fraud URL Intelligence
IP Intelligence

A buyer’s guide to actionable email threat intelligence
and prevent – threats.
Threat Intelligence
Threat InDepth Feeds
Spot cyber attacks before they hit with real-time technical threat intelligence feeds of emerging malware and phishing threats.See how we compare against
Elevate Your Strategy
Download the Complete Competitive Analysis for IP Reputation Now
Threat InDepth Feeds FAQs
What is Cyren Threat InDepth?
Cyren Threat InDepth is an advanced threat intelligence platform that provides real-time, contextual insights into email, web, and file-based threats—helping organizations detect and respond faster.
How does Threat InDepth work?
It analyzes billions of global transactions through the GlobalView™ Threat Intelligence Cloud and correlates data from email, web traffic, and suspicious files to provide actionable indicators of compromise.
What types of intelligence does Threat InDepth include?
It includes phishing and fraud URL intelligence, malware URL and file intelligence, and IP reputation data—covering multiple threat vectors.
Why should I use Threat InDepth instead of standard threat feeds?
Unlike generic threat feeds, Threat InDepth delivers fresh, multi-dimensional, and correlated data with low false positives, enabling faster and more reliable threat detection.
Can Threat InDepth integrate with my existing security systems?
Yes. It integrates seamlessly with SIEM, SOAR, and other platforms like Cortex XSOAR, delivering key indicators directly into your workflows.
What benefits does Threat InDepth bring to a security team?
It helps reduce detection and response times, improves threat prioritization, and enhances overall SOC efficiency by providing deeper visibility into evolving threats.
Is Threat InDepth suitable for enterprises?
Yes. Threat InDepth is built for enterprises that manage complex infrastructures and need proactive, continuously updated threat intelligence.
How is the intelligence updated and maintained?
The system continuously collects, analyzes, and correlates data from millions of global sensors, ensuring the intelligence remains up-to-date and relevant.
Discover More About Threat InDepth Feeds
How Cyber Threat Intelligence Can Protect Your Organization
In a world full of threats, cyber threat intelligence is your defense. To stay ahead of emerging cyber threats, it is crucial to leverage cyber threat intelligence for evidence-based insights...
Read MorePhishing Attack Prevention with Cyren Threat InDepth
What is Phishing Attack Prevention? Phishing attack prevention refers to companies taking security measures in order to prevent phishing attacks on their employees. The measures taken to improve phishing protection...
Read More