Security Operations Centers (SOCs) today operate in an environment defined by scale, speed, and complexity. Enterprises generate enormous volumes of telemetry from endpoints, network devices, identity systems, cloud platforms, and applications. SIEM systems aggregate these signals and attempt to detect malicious behavior through analytics and correlation rules.
The chief information security officer (CISO) plays a crucial role in overseeing security operations, managing compliance, and guiding SOC teams to ensure effective cybersecurity leadership within the organization.
Despite the growing sophistication of security tooling, one persistent operational challenge remains: the gap between threat intelligence and real-time security enforcement.
Organizations subscribe to multiple threat intelligence feeds, deploy SIEM platforms like Microsoft Sentinel, and operate advanced endpoint protection tools such as SentinelOne or CrowdStrike Falcon. However, in many environments, intelligence remains disconnected from enforcement mechanisms. Analysts must manually investigate alerts, move indicators between systems, and determine how threats should be blocked.
Cyber threat intelligence—the process of gathering, analyzing, and applying actionable information about cyber threats, attack methods, and attacker motives—is often not fully leveraged to improve defenses and prevent potential attacks.
In a fast-moving threat landscape, this delay can be critical.
Data443’s Cyren Threat Intelligence and TacitRed Attack Surface Intelligence are designed to help close this operational gap. Through integrations with modern security ecosystems—including Microsoft Sentinel, SentinelOne, CrowdStrike, and Microsoft Defender—Data443 enables organizations to transform threat intelligence into automated defensive action across their security infrastructure.
For SOC teams responsible for protecting enterprise environments, this shift toward operationalized intelligence is becoming increasingly essential.
The SOC Challenge: Detection Without Immediate Enforcement
Security teams today are inundated with alerts. Modern SIEM platforms ingest logs from dozens or even hundreds of sources, including:
- endpoint security systems
- firewalls
- identity platforms
- network devices
- cloud infrastructure
- application telemetry
- monitoring software
- external threat intelligence feeds
Microsoft Sentinel, for example, aggregates these signals and uses analytics rules to detect suspicious patterns such as abnormal login activity, malware execution, or network anomalies. Incident detection is a critical component of early threat identification, helping security teams respond quickly to emerging threats.
However, detection is only the first step.
In many SOC environments, analysts must manually determine:
- whether an indicator is malicious
- whether it is relevant to their environment
- how to block the associated threat
- which systems should enforce defensive actions
This manual workflow creates several operational challenges:
- Alert fatigue
Analysts are overwhelmed by large volumes of alerts. - Manual IOC management
Threat indicators often need to be manually transferred between systems. - Delayed response times
Security teams may take hours—or longer—to convert intelligence into enforcement. - Disconnected tools
Threat intelligence feeds, SIEM platforms, and endpoint protection tools may operate in isolation. - Endpoint detection limitations
Automated endpoint detection tools, such as EDR, may miss advanced threats that require proactive threat hunting techniques to uncover.
Attackers often exploit this gap between detection and enforcement. Even if an organization identifies malicious infrastructure, delayed response allows attackers time to move laterally, escalate privileges, or exfiltrate data.
Effective event management is essential for coordinating detection and response activities, ensuring that security alerts, logs, and incident data are organized for efficient action.
SOC teams increasingly need solutions that allow threat intelligence to become immediately actionable across the security ecosystem. Rapid incident response is essential to minimize damage, and leveraging threat intelligence alongside proactive threat hunting helps security teams identify threats more effectively.
The Data443 Threat Intelligence Platform Ecosystem
Data443 provides two complementary intelligence sources designed to support operational security workflows:
- Cyren Threat Intelligence
- TacitRed Attack Surface Intelligence
These sources are integrated through a threat intelligence platform that aggregates and analyzes threat data from multiple sources to support operational security workflows.
Together, they provide visibility into malicious infrastructure and emerging threats across the internet.
Cyren Threat Intelligence
Cyren Threat Intelligence focuses on identifying malicious activity across global internet infrastructure.
One of Cyren’s most valuable telemetry sources is its large-scale email analysis infrastructure. Cyren systems analyze more than one billion email messages per day, providing insight into emerging phishing campaigns, malware distribution networks, and malicious infrastructure used by attackers.
From this global telemetry, Cyren extracts several key types of threat intelligence:
- IP reputation intelligence
- malicious domain indicators
- URL reputation data
- malware distribution infrastructure
- email threat indicators
Because email remains one of the most common attack vectors for cybercriminals, this dataset provides early visibility into emerging campaigns.
By analyzing patterns across massive volumes of email traffic, Cyren can identify suspicious domains, phishing infrastructure, and malware command-and-control systems before many organizations detect them internally.
This process also includes threat intelligence enrichment, where additional context is automatically added to alerts to improve accuracy and accelerate investigations.
TacitRed Attack Surface Intelligence
TacitRed provides a complementary form of intelligence based on network telemetry and NetFlow analysis.
While Cyren focuses on email and internet infrastructure threats, TacitRed analyzes how systems communicate across networks to identify suspicious patterns and malicious infrastructure.
TacitRed intelligence can identify:
- command-and-control networks
- suspicious hosting providers
- malicious domain communication
- abnormal traffic patterns
- indicators of compromised infrastructure
NetFlow analysis provides a unique perspective because it observes network behavior, rather than relying solely on malware samples or reputation lists.
This allows security teams to detect malicious infrastructure that may not yet appear in traditional threat intelligence feeds.
Bringing Intelligence Into the Security Ecosystem
Threat intelligence alone is not enough to stop attacks. Intelligence must be integrated into operational security systems—including firewalls, anti-malware tools, and monitoring platforms—so it can influence detection and response.
Data443 has developed integrations designed to deliver intelligence directly into modern security ecosystems.
Supported platforms include:
- Microsoft Sentinel
- Microsoft Defender
- SentinelOne
- CrowdStrike Falcon
These integrations enable threat indicators from Cyren and TacitRed—such as malicious IP addresses, domains, URLs, and other indicators of compromise (IOCs)—to flow directly into SIEM and endpoint security environments where they can influence detection and enforcement workflows.
Threat intelligence is integrated with these platforms to proactively identify and disrupt cyber campaigns before they cause damage.
Operational intelligence can also inform the adjustment of security controls such as firewalls, endpoint policies, and access rules, improving overall cybersecurity resilience.
Marketplace-Driven Deployment
One of the major challenges in adopting threat intelligence is integration complexity. Security teams often spend weeks integrating external feeds into SIEM platforms or endpoint security tools.
Data443 addresses this challenge through marketplace integrations designed for simplified deployment.
For Microsoft Sentinel, integrations are available through the Sentinel Content Hub, allowing SOC teams to install connectors directly from the platform.
Deployment typically involves only a few steps:
- Install the integration connector from the marketplace
- Configure Cyren or TacitRed API credentials
- Connect the endpoint platform API
- Enable automation playbooks
Once configured, threat indicators begin flowing automatically into the security environment.
In many cases, initial deployment can be completed in minutes rather than days or weeks.
Architecture: From Intelligence to Enforcement
The architecture of the integration pipeline is designed to operationalize threat intelligence across multiple layers of the security ecosystem.
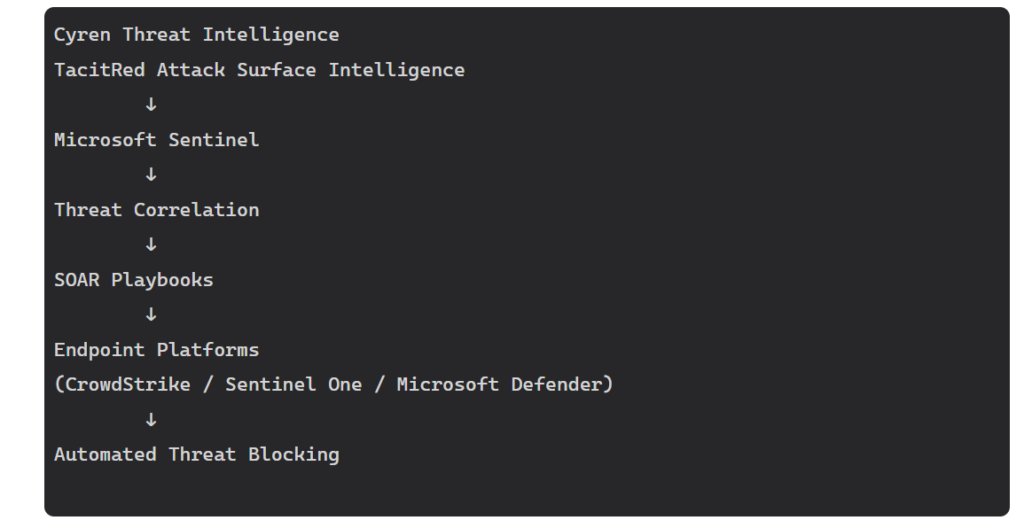
Figure: Automated threat intelligence pipeline from Cyren and TacitRed through Microsoft Sentinel to endpoint enforcement platforms.
In this architecture, Microsoft Sentinel serves as the orchestration layer. Threat intelligence feeds enrich Sentinel analytics, allowing the platform to correlate indicators with security events across the environment. When suspicious activity is detected, Sentinel can trigger automation workflows that instruct endpoint platforms to block malicious infrastructure.
This architecture enables organizations to move from passive threat intelligence to automated security enforcement.
Real-Time Intelligence Distribution
Another critical component of the system is real-time intelligence distribution.
When malicious infrastructure is identified through Cyren or TacitRed telemetry, threat indicators can be distributed immediately to connected security environments through API-based intelligence feeds.
This allows organizations to benefit from intelligence discovered anywhere within the telemetry network.
The result is a collective security effect: detection of malicious infrastructure in one context can quickly help protect other organizations.
For SOC teams, this rapid intelligence sharing can significantly reduce the time between threat discovery and defensive action.
Why Threat Intelligence Quality Matters
Many organizations subscribe to multiple threat intelligence feeds, but more data does not always lead to better security.
In fact, excessive or low-quality intelligence feeds can create operational challenges by overwhelming analysts with irrelevant indicators.
Effective threat intelligence must prioritize signal over noise.
High-quality intelligence requires:
- filtering false positives
- prioritizing active threats
- removing outdated indicators
- delivering timely updates
The engineering teams behind Cyren and TacitRed emphasize that identifying relevant intelligence within massive datasets is one of the most important challenges in threat intelligence operations.
Curated intelligence feeds that focus on actionable indicators allow SOC teams to operate more efficiently.
